Cyber Security Audit
Expert evaluation of an organisation’s cybersecurity resilience
We combine network footprint analysis, source code scanning, and strategic expert interviews to identify hidden risks and deliver actionable security improvements.
Cybersecurity risk: what’s at stake?
Before committing capital, private equity investors need to assess cybersecurity risks as part of their standard diligence process.
A target company’s vulnerabilities, whether from outdated systems, weak data protection, or poor security governance, can result in regulatory fines, operational disruptions, and reputational damage.
Embedding cybersecurity reviews into investment decisions supports financial performance and ensures portfolio companies can scale securely.

Hidden cyber risks: what our audit reveals
Our cybersecurity assessments provide investors with a clear view of a company’s security posture, identifying risks that could impact business continuity and valuation. These insights help investors mitigate risks, ensure compliance, and strengthen the long-term security of their portfolio companies.
External exposure
Identifies vulnerabilities in the company’s digital footprint that could be exploited.
Data leaks and compliance risks
Assesses whether sensitive company or executive information has been exposed online.
Internal security gaps
Analyses source code and internal processes to detect weaknesses that could lead to breaches.
Security governance and risk management
Evaluates the company’s resilience, including backup protocols, infrastructure security, and employee awareness.
They trust our expertise
Our Cyber Security Audit clients
A unique combination of tools, data and experts
A simple process for a thorough cyber assessment
Vaultinum’s approach combines code scans, data and experts analysis to provide deep insights into the tech and overview the full range of an organisation’s IT security infrastructure, policies and governance.
01
Online assessment of cyber-readiness
02
OSS code scan and network footprint
03
Consultation with our experts
04
01
Online assessment of cyber-readiness
- Security governance and risk management
- Data protection compliance measures
- Premises and equipment protection measures
- Network and infrastructure management processes
02
OSS code scan and network footprint
- Identification of free and OS code vulnerabilities
- Identification of OSS vulnerabilities vs NVD and Github
- Inventory of versioning and associated known vulnerabilities
- Review of content for contributors
- Review of integrated commercial code
- Evaluation of theft risk
Penetration test available as an option, upon request.
03
Contextualisation with our experts
- Review findings in context of business objectives
- Identify mitigating factors
- Understand technology environment and end use
- Evaluate potential remedies to formulate a relevant action plan
04
Cybersecurity risk report
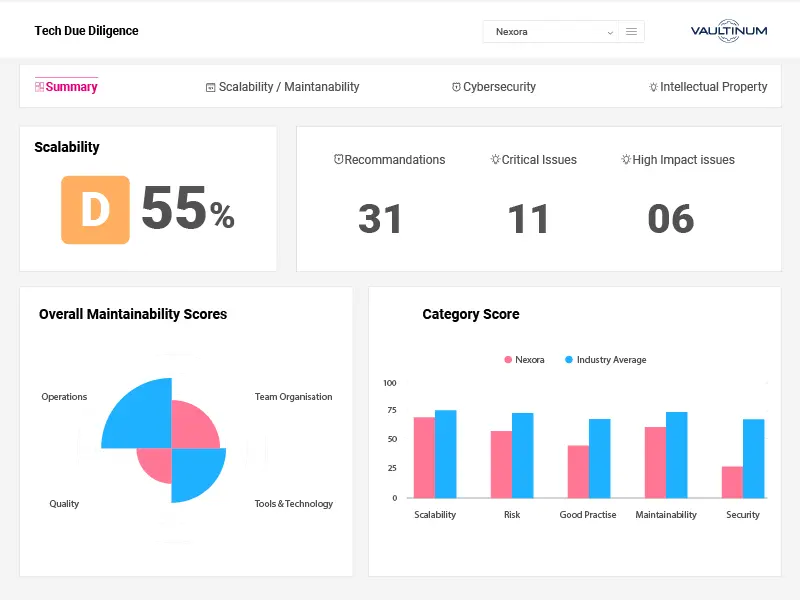
- Overall cybersecurity performance rating compared to industry standards
- Identification of critical cybersecurity risks with tailored remediation strategies
- A structured plan outlining mitigation steps, priorities, and associated costs
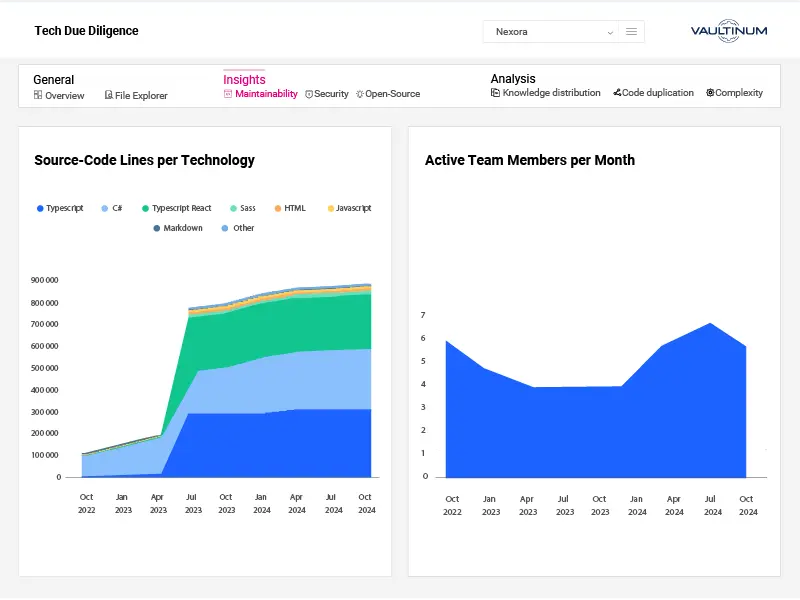
All-in-one platform for tech performance monitoring
Vaultinum’s platform centralises all data relevant to tech due diligence, enabling fund managers to securely access and monitor KPIs post-Tech Due Diligence.
Secure dataroom for confidential document management
Access to online assessments for continuous monitoring
Secure code upload
Detailed code analysis reports
Investor-focused Technology Due Diligence reports
Portfolio view and dashboard for comprehensive performance insights
Cyber Audit Checklist
A cyber checklist to evaluate and enhance corporate cybersecurity for leaders and investors
FAQ about our Cyber Audit
What is a Cybersecurity Audit?
A Cyber Audit is a focused assessment of a company’s cybersecurity posture by examining how well its systems, processes, and teams are equipped to prevent, detect, and respond to cyber threats. It covers both technical and organisational layers, including network and cloud security, access controls, encryption practices, vulnerability management, incident response readiness, and compliance with relevant standards like ISO 27001 or GDPR. In the context of due diligence, a Cybersecurity Audit helps determine whether cybersecurity risks could impact business continuity, data integrity, or reputational standing. It also assesses whether the company’s security practices scale with its growth and whether sensitive data, especially customer or IP-related, is being adequately protected.
Why is a Cyber Audit important?
A Cyber Audit is essential because cybersecurity failures can lead to data breaches, service disruption, regulatory fines, and significant reputational damage, any of which can materially impact a company’s valuation or attractiveness to investors. As digital infrastructure becomes more complex and threat surfaces expand, it’s no longer enough to assume security is “covered” by default settings or cloud providers. A Cyber Audit helps uncover hidden vulnerabilities in infrastructure, access control, and data handling practices before they become liabilities. It’s especially important during fundraising or M&A, where investors want to know not just that a company is growing, but that its growth isn’t exposed to unmanaged cyber risk. A clean, well-documented cyber posture signals operational discipline, protects critical assets, and strengthens trust with stakeholders.
What is included in a Cyber Security Audit?
A Cyber Audit includes a comprehensive review of the company’s cybersecurity controls, infrastructure, and risk exposure, covering both internal practices and external vulnerabilities. We assess areas such as access management, network configuration, data protection measures, encryption practices, incident response preparedness, and compliance with relevant standards (e.g., ISO 27001, GDPR). Our audits also include a network footprint analysis, which maps publicly exposed assets and identifies potential entry points for attackers which is an essential step in evaluating real-world exposure. While regular penetration testing is a best practice, it is not always in place; in those cases, Vaultinum can provide a targeted penetration test as an add-on to simulate external threats and uncover exploitable weaknesses. The result is a clear view of cyber risk posture, including both technical gaps and process-level vulnerabilities.
What are the most common issues found during a Cybersecurity Audit?
The issues uncovered during a Cyber Audit vary depending on the company’s maturity, industry, and growth stage, but some patterns are consistent. Common findings include weak or inconsistent access controls (e.g., shared credentials, lack of MFA), outdated software components with known vulnerabilities, poor segmentation of cloud environments, and missing or underused logging and monitoring tools. From a process perspective, we often see limited incident response planning, unclear data retention policies, or compliance gaps related to GDPR or ISO 27001. Through our network footprint analysis, we frequently identify exposed ports or services that were not properly secured including, forgotten staging environments, misconfigured APIs, or admin interfaces accessible from the public internet. These are often overlooked internally but can create real attack vectors if not addressed. While not every issue is critical, surfacing them early gives companies the opportunity to improve their posture before they become a liability.
What regulations require a Cyber Security audit?
Several regulatory frameworks either require or strongly encourage regular cybersecurity audits, depending on the industry and geographic footprint of the company. In the EU, the General Data Protection Regulation (GDPR) mandates that organisations implement appropriate technical and organisational security measures, and a cybersecurity audit is often the most effective way to demonstrate compliance. For companies operating in financial services, DORA (Digital Operational Resilience Act) and PSD2 impose specific obligations around ICT risk management and incident response. In the U.S., sectors such as healthcare and finance are governed by HIPAA, SOX, GLBA, and SEC cybersecurity disclosure rules, all of which imply or require periodic assessments of cyber risk. Frameworks like ISO/IEC 27001, NIST CSF, and SOC 2 don’t mandate audits per se, but they form the basis for many third-party assessments and are often required by enterprise customers or partners. Even where not strictly mandatory, cybersecurity audits are increasingly expected in M&A, investor due diligence, and large commercial contracts, making them a de facto requirement for any tech-enabled business operating at scale.
What’s the difference between a Cybersecurity audit and a penetration test?
A cybersecurity audit is a comprehensive assessment of a company’s security posture that includes reviewing policies, infrastructure, access controls, data protection measures, compliance frameworks, and incident readiness. It takes a broad view of how well security is built into both the technical environment and the organisation’s processes. In contrast, a penetration test (or pen test) simulates a real-world attack to identify specific vulnerabilities that could be exploited by malicious actors. Pen tests are tactical, focusing on how systems behave under active threat scenarios, whereas audits are strategic, evaluating whether the right security foundations are in place to manage risk over time. At Vaultinum, we often recommend pairing both: the audit to uncover structural or procedural gaps, and the pen test to pressure-test external defences and validate remediation efforts. Each provides a different lens on security, and together they offer a much more complete picture.
How often should a company conduct a cyber audit?
Cybersecurity audits should generally be conducted annually, but the ideal frequency depends on the company’s risk profile, regulatory environment, and growth stage. For businesses handling sensitive customer data, operating in regulated sectors, or undergoing rapid change, such as cloud migrations, product expansion, or M&A activity, more frequent audits may be necessary. If the company is scaling quickly or entering new markets, it’s important to reassess exposure points regularly, as new integrations or system changes can introduce fresh vulnerabilities. Even in the absence of formal regulatory requirements, an annual cybersecurity audit is widely considered best practice both for maintaining a strong security posture and for demonstrating operational maturity to investors, clients, and partners.
Our latest articles on