8 good reasons to use electronic timestamping
With the digitalization of entire sectors of the economy, certified timestamping has become increasingly important in commercial relations as it is one of the best ways to demonstrate that an action has been taken.
This article will explore the many areas where electronic timestamping is useful for proof and traceability purposes.

Although electronic timestamping is mostly used when electronically signing documents, as you will see today, it is useful in many other areas for proof and traceability purposes. Vaultinum, a trusted third party, regularly provides support to its customers through its reliable, adaptable and secure timestamping system.
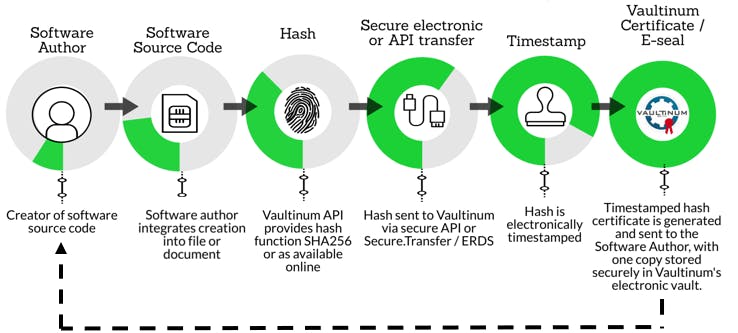
1. Intellectual property
I developed a software. How can I protect myself against possible appropriation by a third party? How can I prove that I developed it before a third party?
According to article L111-1 of the Intellectual Property Code, “the author of a work of the mind shall enjoy in that work, by the mere fact of its creation, an exclusive incorporeal property right which shall be enforceable against all persons.” In other words, and subject to fulfilling certain conditions such as originality, copyright protection exists from the moment a work is created and does not require any additional formality, contrary to a trademark or an invention. This remains true throughout the 179 signatory countries of the Berne Convention.
In the absence of compulsory registration with an office, it can, however, be difficult to provide proof of the existence and the content of a digital creation on a specific date, that is to say before that claimed by a possible infringer. It is therefore recommended to create a so-called “evidentiary repository” with a trusted third party such as a bailiff, a notary, or Vaultinum.
Due to its technology involving the use of symmetric and asymmetric encryption algorithms, hash functions/fingerprint creation and electronic timestamping guaranteeing the integrity of the transmitted elements, the deposit made with Vaultinum:
- materialises the content of the digital creation;
- dates the creation;
- attests to the depositor’s ownership;
- records the content and creation dates.
All preparatory documents necessary to file a patent application can also be filed. Indeed, the procedure for filing a patent with a patent granting authority (such as the European Patent Office, the Federal Institute of Intellectual Property in Switzerland, the National Institute of Industrial (INPI) in France, the National Intellectual Property Office in China or the United States Patent and Trademark Office) is a long and complex procedure which very often responds to the rule of "first come, first served". In this context, the evidentiary repository presents several advantages:
- It limits the risks of appropriation of an invention by partners and/or third parties;
- It affixes a date certain to ideas, projects, preparatory documents, etc. pending validation of a patent application;
- It records the results of research (especially laboratory notebooks) as and when discoveries are made so as to preserve prior rights and ensure a fair distribution of rights between employees;
- It proves that an invention kept secret was developed before a third party filed a patent on it, allowing the inventor to continue to use it (right of prior personal possession).
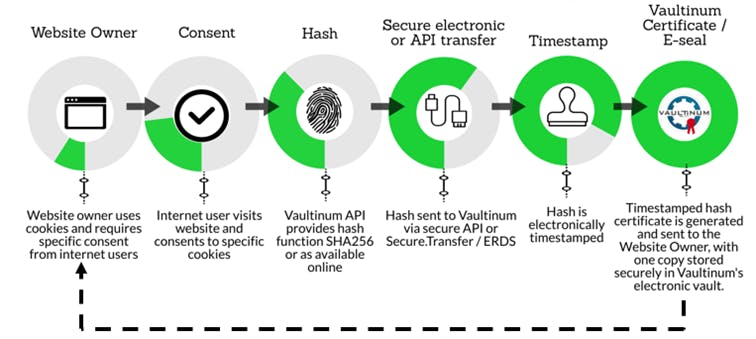
2. Personal data protection
In accordance with the GDPR, I use the email addresses of prospects to send them offers if I have their prior consent. I also delete this data three years as from the last contact with the individual concerned. In the event of a CNIL control, how can I prove my compliance with the GDPR?
- Provide proof of consent
In cases where the legal basis for processing is consent, the data controller must be able to demonstrate that the data subject has given consent to the processing of personal data concerning them.[1]
In practice, compliance with this obligation can be complicated as the text does not specify how this evidence can be reported. It is therefore essential for the data controller to be equipped with a tool ensuring the conservation and traceability of the following elements:
- the content and date of the consent;
- the means used to give consent;
- the information communicated at the time of consent; and
- if applicable, the date of withdrawal of consent.
On this point, the French Data Protection Authority (CNIL) indicated, in March 2017, that "the digital timestamping of the indication of consent (by means of a click or a ticked box) and the implementation of a procedure for obtaining consent, duly documented, must be considered as a valid means of establishing proof of consent”.[2]
Vaultinum offers a reliable, adaptable and secure solution for timestamping and automated archiving thanks to its API. In addition, Vaultinum is a partner of CMP (Consent Management Platform) and as such, ensures the timestamping and, if necessary, the archiving of consent records.
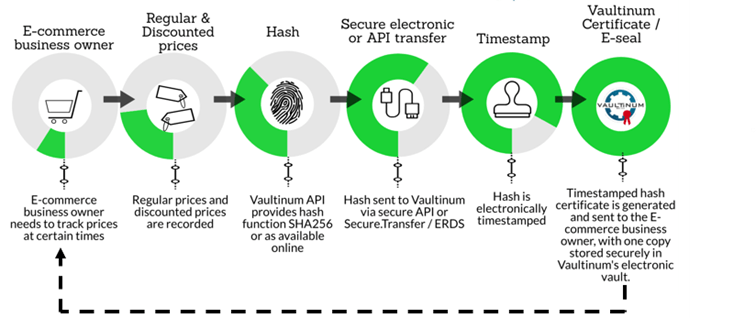
3. Electronic commerce
As a businessperson, I offer discounts on certain items sold on my e-commerce site. Regulations require me to justify the reference price from which the reduction is applied. How can I do this?
The authenticity of discounts offered during promotional operations is assessed with regard to unfair commercial practices (Article L. 121-2 to L. 121-5 of the Consumer Code). Price reduction announcements to consumers are governed by the decree of 11 March 2015.[3] Under article 2 of this decree, sellers are required to indicate, in addition to the announced price reduction, the reference price on the basis of which the announced reduction is calculated.
Although professionals are free to determine the reference price of their choice (for example, regular price, competitors’ price, recommended price), they must be able to "justify the reality of the reference price on the basis of which the price reduction is announced”.[4] To do this, they may use notes, slips, order forms, sales receipts, catalogues, advertising leaflets or any other documents; all the means of proof first set out in the circular of 7 July 2009 specifying the provisions of the decree of 31 December 2008 (repealed)[5]. However, these means are costly and difficult to execute, especially when price reductions are offered online and repeatedly. They also necessitate tremendous data collection and evidence-based archiving.
With a view to limiting the impact of these regulations and simplifying the application of price reductions, professionals are recommended to use an automated timestamping tool to ensure the preservation, traceability and integrity of the following elements:
- the chosen reference price (example: price applied by a competitor);
- the location of the chosen reference price (example: a website page);
- the date of application of the chosen reference price.
The implementation of reliable and recognized means of proof to justify the reference price is all the more important as the General Directorate for Competition, Consumption and Fraud Control (DGCCRF) has for several years now, been closely monitoring online sales and particularly misleading price reduction announcements, as can be seen from its recent surveys.[6]
Vaultinum provides support to e-commerce companies by offering them a turnkey solution for timestamping and archiving proof related to the applied reference price. Through this adaptable, reliable and secure solution, the e-merchant can connect to an API and thus manage thousands of data at a time, in an automated manner.
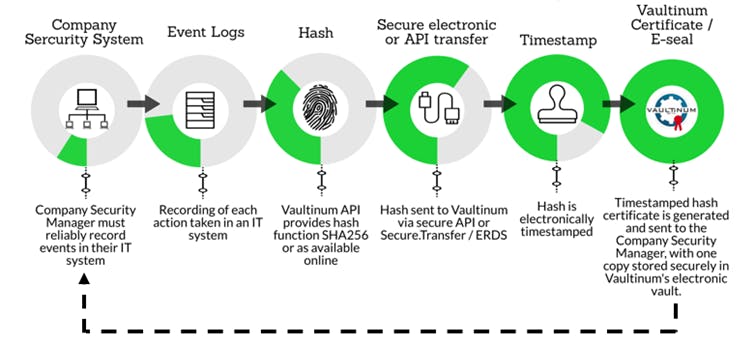
4. Information Technology
An employee repeatedly logged on to sites expressly prohibited by the company’s IT charter. How can I prove this in a reliable way?
Whether human or technical, each action taken in an IT system is likely to leave tracks which must be recorded. These could be:
- successful connection to an application;
- access to a file or to the internet;
- attempted intrusions into the information system;
- application requests.
The National Information Systems Security Agency (ANSSI) emphasizes that event logs are an essential technical component to manage the security of information systems. However, these can serve as evidence only if the log files reliably connect certain events to a particular point in time.
To ensure this reliability, events cannot be timestamped through sole use of the computer's internal clock, as this is easily falsified and deviates naturally over time. The ANSSI first recommends synchronizing the clocks of IT equipment with several internal time sources that are coherent with each other, themselves synchronized with several reliable external sources.[7] Secondly, a logging system must be set up in accordance with applicable regulations and the recommendations of the CNIL insofar as the main objective of logging is to allow the person or the equipment causing an event to be identified directly or indirectly. Finally, logs must be signed and timestamped as soon as they are created so as to ensure their integrity.
5. Supply chain
As a large-scale distributor, I would like to ensure the traceability and transparency of some of my products of animal origin. How can I do this?
Following a number of scandals that testified to a lack of supply chain transparency in the food industry, regulation no. 178/2002 of 28 January 2002 introduced a requirement for food traceability at all stages of production, processing and distribution[8] in order to identify sources of contamination more quickly.
In terms of supply chain (agro-food, luxury goods, wine, pharmaceutical industry), electronic timestamping and, more generally, timestamping applied to "blockchain" technology (a chain of records keeping track of a set of information, in a decentralized, transparent and secure way), has a real potential to ensure traceability and control of the origin of a product.
At every stage of the supply chain (producer, processor, distributor), a certain amount of information (dates, origin) concerning a food product, from its manufacture to its sale, will be recorded in a timestamped blockchain register. Depending on the case, the recording on the register could be done either by means of human intervention such as a photograph of the items, or automatically, through the use of connected sensors. Each actor in the supply chain can access the blockchain register to learn the identity of the person who first entered the information, the content of information itself (the integrity of which is guaranteed), and the date of registration of this information.
And yet, blockchain has its limits. Distributors and other importers need to protect their commercial networks and other trade secrets. The transparency of blockchain prevents this protection, but another solution exists. It consists of validation by a trusted third party by virtue of the presence of secure, timestamped register systems at each stage of the supply chain.
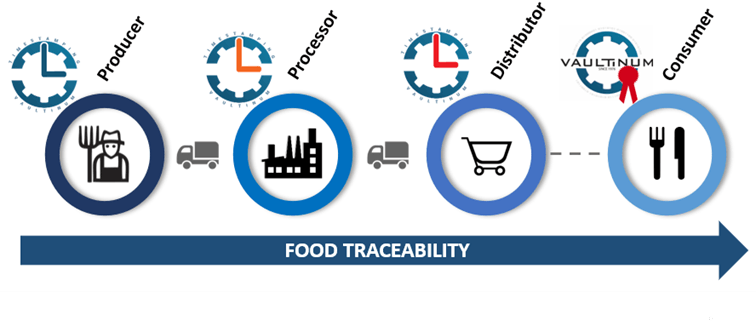
The same question arises with regard to environmental protection. Soon, food and product traceability will allow for the display of information on the environmental footprint of a product.
In terms of supply chain (agro-food, luxury goods, wine, pharmaceutical industry), electronic timestamping and, more generally, timestamping applied to "blockchain" technology (a chain of records allowing to keep track of a set of information, in a decentralized, transparent and secure way), has a real potential to ensure timestamping, traceability and control of the origin of a product.
At every stage of the supply chain (producer, processor, distributor), a certain amount of information (dates, origin) concerning a food product, from its manufacture to its sale, will be recorded in a timestamped blockchain register. Depending on the case, the recording on the register could be done either by means of human intervention such as a photograph of the items, or automatically, through the use of connected sensors.[1] Each actor in the supply chain can access the blockchain register to learn the identity of the person who first entered the information, the content of information itself (the integrity of which is guaranteed), and the date of registration of this information.
And yet, blockchain has its limits. Distributors and other importers need to protect their commercial networks and other trade secrets. The transparency of blockchain prevents this protection, but another solution exists. It consists of validation by a trusted third party by virtue of the presence of secure, timestamped register systems at each stage of the supply chain.
In practice, a leading European brand has already chosen blockchain timestamping for its chicken industry. Each actor in the supply chain can enter and timestamp traceability information which is of interest to them, and which will, for the most part, be communicated to the consumer by means of a QR Code[2].
Vaultinum provides support to its clients in setting up a timestamping system to date the events registered throughout the supply chain. Using the Vaultinum API, client or blockchain systems can interface with Vaultinum’s timestamping solution and continuously and automatically timestamp thousands of events in a reliable, secure and adaptable manner.
6. Quality assurance and monitoring of document versions
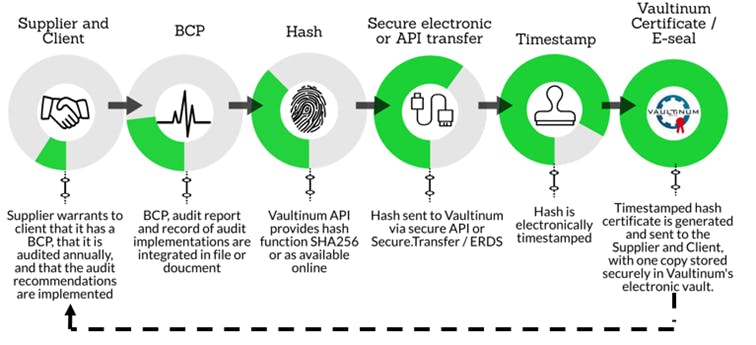
To play it safe, my service provider has put in place a business continuity plan ("BCP") to manage force majeure or crisis situations. This BCP is essential for my business. It is updated every year. How can I be sure that the plan I have is the latest version and that it has not changed?
Business continuity plans (BCPs) have long been required by buyers of products and services. These plans are generally tested and updated annually. They are essential because they provide information on the measures taken to avoid service interruptions on the supplier's side, for example, in the event of unforeseeable events or natural disasters and, and in turn, on the buyer's side. As such, it is essential that tests and updates are timestamped and securely archived in order to maintain documentary evidence over time and ensure the legal protection of all parties concerned.
Vaultinum provides secure and reliable archiving and timestamping services.
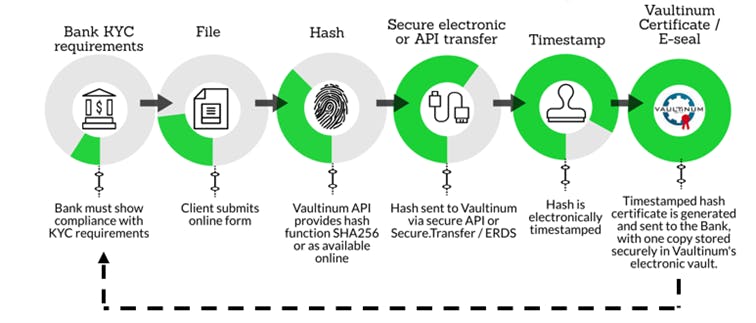
7. Banking and insurance
Data and information are often submitted online and are sometimes used to generate positions, offers or assessments. In order to avoid any dispute related to the content of the information submitted and its date of submission, and to guarantee that requests are dealt with properly and within a given timeframe, content should be archived securely and with a timestamp token.
Vaultinum supports banks and insurance companies by offering them a turnkey solution for timestamping and secure archiving of online requests. This adaptable, reliable and secure solution enables the automation of certified timestamping and secure archiving, thanks to the Vaultinum API.
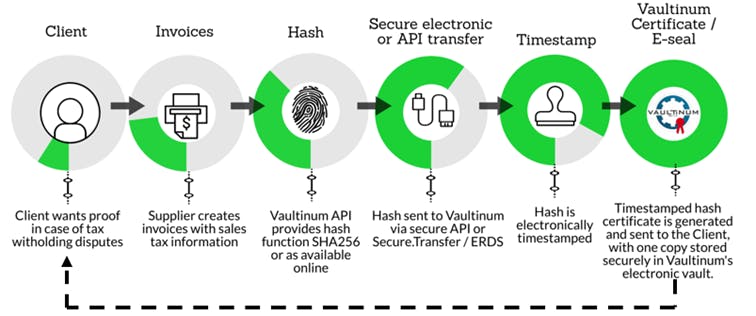
8. Invoicing
Invoicing has a number of consequences, particularly in terms of payment deadlines but also with regard to deadlines for taxes and other fees. How can I make sure that I can provide proof of electronic invoicing and the date it was issued/sent?
The digitalization of invoicing processes promises significant efficiency gains and cost reductions. At the tax level, article L 102 B of the French Tax Procedure Code, amended by article 16 of the Amending Finance Law for 2016 allows taxpayers to digitize their paper invoices received and issued and to keep them in digitized format for the fiscal retention period of 6 years. The regulations specify that digitized invoices must meet two conditions; they must be secured to ensure their integrity, and they must be timestamped.
Although the timestamp can be internal, a timestamp certified by a trusted third party or a qualified timestamp process is essential to avoid disputes, especially since the timestamping of invoices is also used to enforce payment deadlines and calculate late payment penalties.
Vaultinum has developed an API to which clients can connect to obtain an automated certified timestamp of each document with the additional possibility of secure archiving.
Conclusion
With the digitalization of entire sectors of the economy, certified timestamping will become increasingly important in commercial relations since it will be the best way to demonstrate that an action has been taken. In addition, electronic timestamping does not only affix a date to a document, it also attests to the integrity of the content of the document it dates, which is a definite evidential advantage.
If you would like more information on the services offered by Vaultinum in the area of timestamping, you can contact the legal department at the following address: legal@vaultinum.com.
[1] Regulation (EU) 2016/679 of April 27, 2016 on the protection of individuals with regard to the processing of personal data and on the free movement of such data and repealing Directive 95/46/EC, art. 7.
[2]Commission nationale de l’informatique et des libertés, Consultation publique sur le règlement européen, mars 2017.
[3] Decree of 11 March 2015 relating to price reduction announcements to consumers.
[4] Ibid., art. 3.
[5] Circulaire du 7 juillet 2009 concernant les conditions d’application de l’arrêté du 31 décembre 2008 relatif aux annonces de réduction de prix à l’égard du consommateur, p. 6.
[6] Communiqué de presse, Pratiques commerciales des enseignes de vente en ligne : la DGCCRF a transmis à l’autorité judiciaire les conclusions de ses investigations concernant le site vente-privee.com, 10 janvier 2019.
[7] Agence nationale de la sécurité des systèmes d’information, Note technique – Recommandations de sécurité pour la mise en œuvre d’un système de journalisation, 2 décembre 2013.
[8] Regulation (EC) No 178/2002 of the European Parliament and of the Council of 28 January 2002 laying down the general principles and requirements of food law, establishing the European Food Safety Authority and laying down procedures in matters of food safety, art. 18.
[9] Etude réalisée par Blockchain Partner, Supply Chain, Traçabilité & Blockchain, 10 juillet 2017.
[10] Dalila BOUAZIZ, Carrefour lance la première blockchain alimentaire d’Europe, E-commerce mag, 6 mars 2018.

Recommended for you


